Blogs
Blogs
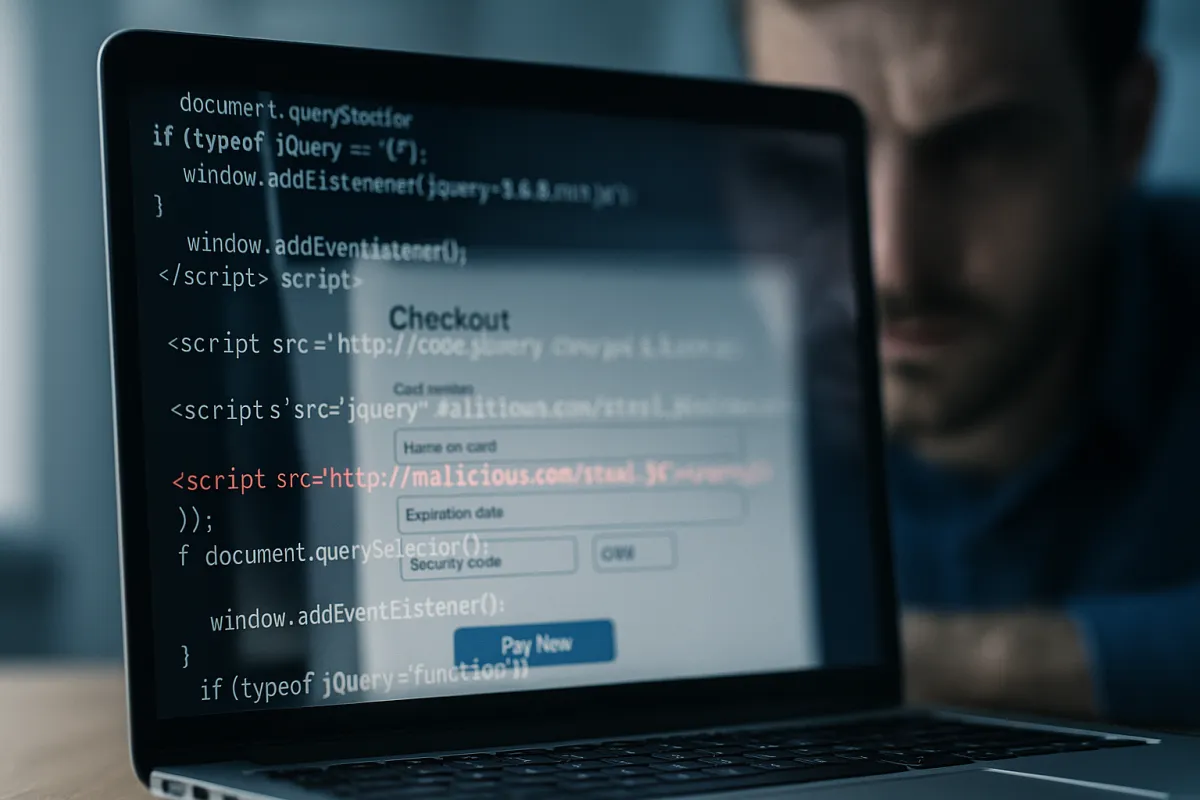
Pixels: The Silent Hacking Threat in Your Payment Page
One invisible script could cost you every customer you’ve ever earned.
You double-check your bank account and balance invoices and receipts. Everything looks good.
No chargebacks. No weird logins.
But then a customer emails you stating “I used my card on your site last week… and now I’ve got $3,000 in charges I didn’t make.”
You check your systems. No red flags. No alerts. No breach notifications.
There’s no indication that your login credentials were stolen.
But someone was on your site, slipping in with a back door opened by a single line of invisible code. A script was all it took to silently steal everything.
Welcome to the New Era of Digital Skimming
Most people have probably heard of phishing and ransomware.
Some may be aware of skimming where hardware takes the embedded info from a credit card’s magstripe.
But have you heard of script skimming?
This particular threat doesn’t lock you out or crash your site.
It hides in plain sight, recording in real time, every keystroke on your checkout page including credit card numbers, names, CVV codes, and billing addresses.
Most businesses don’t even know they’ve been hacked until customers complain.
What Makes Your Website Vulnerable?
You might have thought you were safe, thinking “I don’t store any card info and I use a trusted payment provider! “
That’s great, but not enough anymore.
Today’s attackers don’t go after your payment processor. They go after you via your checkout page, your scripts, your iframe, your marketing pixel, your plugin.
“In 100% of confirmed skimming attacks, the malicious script was on the merchant’s site—not the processor’s.”
~ SecurityMetrics Forensics Team, 2024
No one is even suggesting that it was you or your website contractor placed bad code. It could’ve come from:
A plugin you installed six months ago
Something added to an API to pull in malicious code.
The wrong link clicked in an unsuspicious email.
A social media pixel that loads a third-party script
A 3rd-party script someone added for legitimate tracking, but forgot about
Even worse? That one script could load another script… which loads another script… which hides the attacker. These multi-layered script chains bury themselves deep inside those it victimizes.
And once they’re in, they don’t ask for permission.
They just listen. And silently skim.
Why PCI 4.0 Is Changing the Game (And Why You’ll Be Required to Catch It)
Two powerful new rules in PCI DSS 4.0 became official as of March 31, 2025, :
1. Requirement 6.4.3 — Script Authorization
You must identify, inventory, and approve every script that runs on your payment page.
That means you must:
Know where each script came from
Know what it’s doing
Be able to prove that you approved it
2. Requirement 11.6.1 — Script Monitoring
You are also responsible for monitoring your site in real-time to detect if new scripts appear.
This isn’t optional, and this isn’t “for big businesses only.”
This is required for anyone who uses a website to accept payments.
“Most small merchants never realize they’re vulnerable until it’s too late. These rules exist because the evidence is overwhelming.”
~ Gary Glover, VP of Assessments at SecurityMetrics
What Happens If You Ignore These Requirements?
Let’s keep it real:
💥 A single skimming incident could result in:
Full PCI forensic audits
Mandatory customer breach notifications
$10,000–$100,000 in investigation and remediation costs
Loss of credit card processing privileges
Damage to your brand reputation that takes years to rebuild
And the worst part?
Many businesses pass their audit… and still get breached because they never implemented ongoing script monitoring.
A PCI SAQ (Self-Assessment Questionnaire) is just a single point-in-time check.
What happens every day after that is what matters most.
How Script-Based Attacks Work (in Plain English)
Let’s simplify this:
You install a tracking script such as Google Analytics or a Facebook or chatbot pixel.
That script loads fine… but also loads another helper script from a different site.
That second script (or a third one it loads) includes a small line of malicious JavaScript code.
That malicious script reads what users type into your checkout page… in real time.
The attacker gets every card number as it’s typed, even before it’s encrypted by your system and transmitted to the credit card processor.
The scary part?
You, more often than not, can’t see this script by simply visiting your site.
It might only run:
On certain browsers
After a certain delay
On mobile devices
When triggered by the final “Submit Payment” click
What Script Monitoring Actually Looks For
You’re not alone thinking, “Wait, how do I even monitor this stuff?”
Here’s what a PCI-compliant script monitoring solution needs to do:
Run dynamic scans, not just static ones
Complete full test purchases to monitor behavior at each checkout step
Analyze the Document Object Model (DOM), which is where these hidden scripts live
Alert you immediately if an unknown or unauthorized script appears
Offer a full log of events and visual evidence if a breach is detected
It’s not about locking down your site. It’s about watching the right things, in the right places, at the right time.
How a Cheap $4 Plugin Created a $40K Nightmare
A Composite Case Study Based on real-world forensics patterns reported by Sansec and SecurityMetrics.
A boutique wellness brand used a trusted CRM integration with a simple widget that tracked customer browsing.
There were no issues for months until an update to that widget introduced a dependency on a third-party script. Somehow, somewhere, and unbeknownst, that script got hijacked by cyber attackers, who embedded a one-line skimmer into its codebase.
After six weeks, the boutique was responsible for:
Notifying 1,200 affected customers
A $40,000 forensic investigation and remediation fee
5 months of reputation repair
And all of it stemmed from a $4 plugin.
Sources:
According to a RiskIQ Report, in 2018, Magecart attackers injected malicious JavaScript into third-party scripts used by British Airways and Ticketmaster, compromising thousands of credit card transactions and resulting in estimated damages consisting of a $230M GDPR fine
Sansec Research regularly documents ecommerce skimming attacks that originate from compromised third-party tools (e.g., widgets, analytics scripts).
In 2024, SecurityMetrics reported over 2,000 forensics cases in which 100% of skimming scripts were found on merchant sites, never the payment processor.
What To Do Next: A Script Safety Checklist
Here’s how to protect your site, and your customers, starting today:
1. Take Inventory
List every third-party script you’ve added to your checkout page. Dev tools or your developer should be able to provide you with a list.
2. Approve & Document (PCI 6.4.3)
Make sure you have a document stating:
What the script is
Who approved it
Why it’s needed
3. Implement Monitoring (PCI 11.6.1)
Use a PCI-compliant script monitoring tool like:
SecurityMetrics Shopping Cart Monitor
Source Defense
Tala Security
These tools simulate transactions to catch changes dynamically.
4. Make It Ongoing
This isn’t a one-time scan.
Monitoring must be continuous, and alerts must be investigated promptly.
If your business has low volume, PCI allows for weekly scans (but document that too!)
Protecting Trust Starts Behind the Scenes
Let’s face it:
You can’t protect what you can’t see.
But now you know the truth:
These invisible threats are real.
The PCI Council has made monitoring mandatory.
Your business is responsible even if the attacker came through someone else’s code.
The good news?
You’re not alone.
Start by inventorying your scripts.
Talk to a certified QSA (Qualified Security Assessor)
Choose a monitoring solution.
And remember It only takes one line of code to destroy everything you’ve built.
Yes, this is probably an expense you never thought of.
It’s like insurance.
You don’t buy auto insurance just to go out and purposefully wreck your car. You get insurance in case an accident occurs so that you are protected from the financial liability that might occur.
How to Protect Yourself (Before It’s Too Late)
1. Know What You Don’t Know
Assuming you’re exempt is the first step to being exposed.
Instead: Get clarity.
2. Treat Compliance Like Insurance
You don’t need everything today—but you need a roadmap to stay protected.
3. Book a Discovery Call With Experts Who’ve Seen It All
Let us walk you through your risks, your blind spots, and your path forward.
This isn’t about fear. It’s about freedom.

The success stories and results displayed on this website serve as examples of our past work and capabilities. While we strive to deliver exceptional outcomes for all our clients, we cannot guarantee specific results, as individual circumstances and performance can vary. By using our services, you acknowledge that results may differ, and no guarantees are provided.
